The 10 most popular cyberattacks used against companies
Do you know the most common cyberattacks and do you know how to protect yourself from them?
Nowadays, the Internet is a huge part of our everyday life and we can count millions of web users that are using internet for personal or professional matters. The web gathers our most personal data but it’s not danger free yet. In the digital era, it’s essential to be as careful as it can be to not fall into hackers’ traps. To help you recognize those online threats, let’s study together what are the ten most popular cyberattacks.
1. Phishing

Phishing is an attack very well known that steals the identity of someone or an organization that you trust in order to gather confidential information such as your credit card number or your password. The hacker writes then an email that leads you to believe that it comes from a reliable source, misguiding the victim.
There is also a variant of phishing called “spear phishing”. Spear phishing is nothing else than a regular phishing particularly except that it’s very targeted. It is a very dangerous because the hacker can steal the identity of someone you trust by writing messages with some personal information or make an exact replica of an official website in order to make you enter your credit card number.
To avoid those traps, it is important to study carefully the emails that you receive, namely, if it seems suspicious, do not click on the links but try to understand it and see if the URL has the HTTP abbreviation, that will mean that the website is safe. In order to defend yourself from those threats, don’t give away any personal information by email. For example, if your bank asks for your password, check first with them if they really did send that request. It’s also very common to receive this kind of emails in your professional mailbox. In this case, do not click on any link without your superior’s prior consent. You need to take every precaution necessary to not lose company’s data.
2. The man in the middle
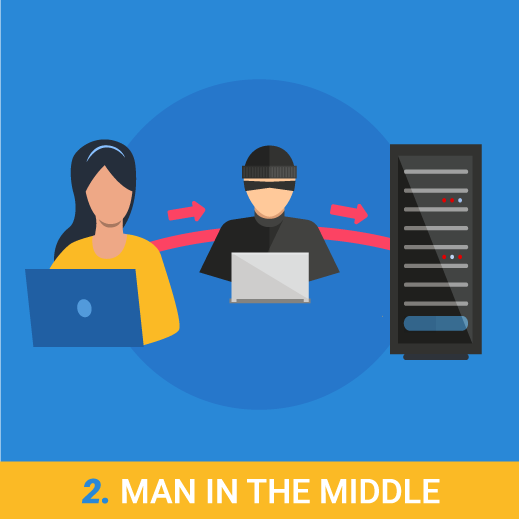
The man in the middle is an attack in which the hacker is the man that intercepts the communication between two people. The man in the middle poses as one of the two persons communicating in order to receive messages. He will send the received information to the true recipient. Thus, both interlocutors are not aware that they have been spied on.
This attack can also be performed by stealing an IP address or by hijacking a session in order to get your cookies information.
A very effective way to perform a man in the middle attack is to simply create their own WIFI connection. This way, as soon as you connect your phone or laptop on this network, the hacker can get to all your personal information.
The hacker can as well do a replay attack by intercepting old messages and send them again posing as the original recipient, or by collecting information and sending them as they are. This is especially the case when the hacker is collecting usernames and passwords for example.
To counter those attacks, you can encrypt the navigation between the network used and the machine from which you are logging in. You can also get a firewall to ensure a safe navigation and an up to date software.
3. Drive By Download

Drive by download is a common way to spread malware on the internet by the means of involuntary download. Even if you are allowing the download, a malware can be downloading itself without you knowing it.
The safest way to protect yourself from it is to stick to reliable websites and to avoid keeping too many programs on your machine that you don’t use. It is very important to raise awareness of your employees about the danger of the drive by download to your employees and teach them how to avoid it because this threat can represent a great waste of time and money. If you don’t have time or the skills for it, you can ask the Ziwit Academy to send you their team of expert to teach and train your staff on this matter.
4. Denial of service attack or distributed denial of service attack

A denial of service attack will disrupt the server in a way that will deny the access to its user. There are two ways to carry out correctly this attack: we drown the server with so many request until it cannot answer them or we take advantage of the system weaknesses. The real goal here isn’t to steal or modify confidential information but to harm the company’s reputation by stopping or delaying its activity. The protection against this attack is tricky but still represents a great stake because of the money that the company may loose if its activity stops completely. In this case, prevention is difficult because a denial of service uses regular web protocols and stopping it would only cut off the normal means of communication. However, we can always be aware of some unusual behaviors by monitoring the traffic and the integrity of a package.
The distributed denial-of-service attack is very similar to a DoS attack, but its difficulty lies in the fact that the attack is performed by various devices at the same time. Therefore, the attack is almost inevitable and very hard to countervail.
5. Password cracking

This attack uses a software that tries several combinations in order to find the right password. There are two different ways for this: one called “brute force” that will try every combination including special characters, numbers and letters, but this method takes a lot of time so the best way to crack a password is the one called “by dictionary”. The attack by dictionary tries the most popular combinations from words that already exist. That can be phrases or words from the dictionary.
The most efficient way to fight against this attack is to use a password containing at least 14 characters that includes special characters, numbers, letters lower and upper cases. It is also very important to not use the same password for everything, they must be all different. It’s up to you find a proper way to remember them all.
6. Ransomware

A ransomware is very popular among hackers. With this software, the hacker can encrypt their victims’ data and then ask for ransom in exchange of their decrypted data.
To avoid such attack, make sure you always have your data backed up on an external hard disk but most especially, never open a file that you’d find suspicious. Those files can have the following extensions: .pif, .com, .bat, .exe, .vbs, .Ink.
7. Malware or malicious software attack

There are so many types of malware whose only goal to compromise your entire system. Among these malware, there is the famous Trojan horse that can start attacks. The type of software that is not to be underestimated is the one called injectors, which can install viruses on computers without being noticed by anti-viruses. We can also mention macro viruses that infect some applications when you open them. Macro viruses are dangerous because they can replicate in order to infect all the applications in your system.
To fight these malware, it’s important to have an up-to-date antivirus. However, if you adopt the right behavior, you can easily avoid being attacked. First of all, think twice before opening some attached files in an email or before clicking on a download link, and limit the sharing of your files.
8. Cross site scripting attack

A cross site scripting attack inserts a software inside the website. When the victim opens the website that contains the malicious script, the user’s information such as cookies, are immediately sent to the hacker. Thanks to the data gathered by cookies, the hacker can also hijack the session or in the worst case scenario, the hacker can get access to screenshots of the victim or they can even register what the victim typeson their keyboard, and thus, collect more information.
To defend yourself against these attacks,youcan treat the whole HTML code before sending them to the web browser. But there is another solution that would be far less tiring, it’s to use the Security vulnerability scanner that detects cross site scripting shortcomings.
9. SQL injection attack

The SQL injection attack mainly targets websites that have a database. So, if the developer doesn’t pay attention to the configuration in the SQL request, the hacker can access the whole database and even modify it. To avoid this, you only need to cancel all the accounts with no password, to cancel useless users, to limit access to certain accounts or to constantly control the input data. However, if this seems too much of a hassle for you, you can still use a vulnerability scanner that will detect for you all the SQL shortcomings.
10. Active or passive eavesdropping attack

Those eavesdropping attacks are made possible by introducing yourself in the network traffic allowing the hacker to steal important and confidential information such as passwords or credit card details. There are two types of eavesdropping attack, one called “passive eavesdropping” when the hacker listens to the information shared on the network and the “active eavesdropping” when the hacker, to get all the information, takes the identity of someone you trust and sends requests to the interlocutors.
Active eavesdropping is harder to detect because to do so, the hacker needs to eavesdrop first in a passive way in order to identify someone he could steal the identity from. The most efficient way to fight this kind of attack is to encrypt your data.
This non-exhaustive list only summarized the most common cyber attacks and there are still so many more types of attacks that we know of for being a real danger for your websites or apps. Each way to attack your system is very specific, you’ll never be completely safe as long as your information system is not equipped with a security software. It’s not something that you take lightly especially when you possess some highly confidential information. These attacks don’t only target people and their credit cards, but many companies are now witnessing the risks that they take if their system is not protected. There are many examples in which a company whose clients’ details have been stolen made the company lose a very big amount of money.
Cybersecurity is still a distant notion for a lot of us, but it doesn’t make it less important to understand its issues. We are currently living in atime where we go through the internet for absolutely everything, this is why we must protect every data that we process. Being protected against a cyberattack is the duty of every company that owns someone else’s information. Whether it’s a big corporation or a small company, they all own a website or an app that might get hacked. It would a good idea to raise awareness of your employees about cybersecurity and how to use safely internet in order to avoid being attacked or you can use a vulnerability scanner to identify shortcomings on your website or app, thus you’ll be sure to stay protected.
