Why should my company carry out security audits on a regular basis?
The best way to guarantee a perfect security of your infrastructures is to frequently carry out security audits. We’ll explain to you why this step is essential!
What is a penetration test?

It can never be repeated enough: cybersecurity is essential for a company! To guarantee the security and integrity of your information system, there’s only one way: carrying out pentests on a regular basis.
If you don’t know the first thing about cybersecurity (we won’t hold it against you 😉), a pentest is an audit of your structure performed by cyberexperts.
The pentesters are entrusted with the difficult task to perform penetration tests in order to find any existing breach or vulnerability, without damaging or affecting your IT system integrity.
These breaches may be technical and affect your IT infrastructure, leaving you in the grip of wild hackers (yes, just like a Pokémon!)
Other human breaches can be a real pain in the neck for your company. For instance, a reckless coworker can be the target of social engineering or a phishing campaign.
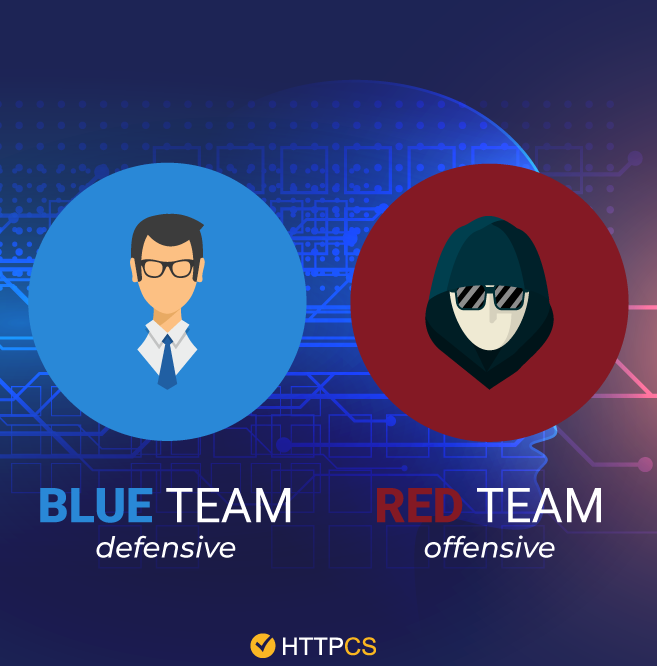
These tests mentionned above are considered as “offensive”. They’re carried out by pentesters called “Red Team”. Don’t get the wrong idea: these pentesters are not dressed with a red jersey…
When it comes to the protocols and procedures of protection or crisis management, the audit is carried out by the “Blue Team”, also called “defensive team”.
After the audit, a cybersecurity report will be sent to you. It will mention corrective measures to apply in order to achieve a satisfactory safety level and to ensure compliance with some of these standards: ISO 27001, 27002, PCI-DSS, HIPAA…
If you don’t know which company to choose to carry out these audits, we’re going to break the back of the work for you: choose the Ziwit Consultancy Services! This certified and reputed organization put at its customers’ disposal passionate and experienced IT experts. They will help you with your audits, along with ensuring compliance with the main security standards, and even legal standards, like the GDPR.
Ziwit is committed and does its best efforts to help any kind of company or organization reach their goals. And if you’re not sure about the Ziwit Consultancy reputation, several companies like Lagardère, Sanofi, Adobe and TF1 currently trust us.
Even though they’re extremely efficient, nothing’s infallible in this world… Consequently, these “manual” and occasional audits are facing some limitations.
What are the limits of an occasional human audit?
The report sent to you after the audit is like a “depiction” of your cybersecurity situation in the moment. And in case you were wondering: no, we don’t really send a picture. It was just an “image” (while I’m at it, I might as well stick to the lexical field of photography) to say that we spend a lot of time drawing up a representative report of your IT security.
However, this situation may be disrupted by an inclusion/modification of some content on your system or network infrastructure, or by a breach that occured after your audit report was sent to you.
A new security breach may indeed occur if you change your IT infrastructure, your provider, or even your employees with an insufficient level of awareness.
These recent vulnerabilities can also come from your software. For instance, a new update of your CMS (Content Management System) or operating system (OS) can lead to a new breach. They can also come from new hacking methods that are constantly improving: these are 0-day breaches. If you’re a cybersecurity initiate, 0-day is pronounced “Zero-Day”.

A 0-day breach is exposed to the public only when it is listed within the CVE (click on the hyperlink and you will know everything about this word 😉). In the meantime, without any daily scan or monitoring performed, your company, your sensitive data and your customers are vulnerable.
This disaster scenario would lead to a loss of trust from your customers, a sharp decline of your income or even legal consequences. In short, that situation would make your face look like an impression of the The Scream by Edvard Munch.
How HTTPCS can help me improve my protection?
Don’t worry! In order to make your company and your data more secure, there are automated audit tools in the world of cybersecurity known as “Web Vulnerability Scanner“, from the Security module.
For the record, Security is the web vulnerability scanner created by HTTPCS. This new generation scanner reports all the breaches contained within a web application, and carries out an audit of that application thanks to its 100% mapping technology. If you didn’t understand these technical terms, it’s okay. Just remember that it’s a robot that detects security breaches on a website or web application.
Security also has a breach simulator that guarantees a zero false positive rate and only reports exploitable breaches.
The advantage of this solution is to audit websites or web applications on a daily or weekly basis.
These vulnerability scanners work with robots or “Virtual Agents” (yes, they’re not real. We haven’t created a physical robot yet). These robots are fully familiar with all the CVE vulnerabilities and are able to detect 0-Day breaches because they learn from the breaches contained within the OWASP Top 10.
After each audit, a detailed report lists the vulnerabilities of a website, and gives a clear indication of their criticality levels and the fixes to apply.
These countermeasures are useful if you want to correct your vulnerabilities one by one with efficiency.
In addition to its vulnerability scanner, HTTPCS can provide three additional modules:
- Integrity by HTTPCS : An integrity checker equipped with the latest technologies in order to prevent any fradulent change of a content or the insertion of malicious files on your website or web application.
- Monitoring by HTTPCS : A web monitoring solution that sends you a notification in case of service loss thanks to an infallible system predefined within your website.
- Cyber Vigilance by HTTPCS : Web, Deep Web and Dark Web monitoring solution to keep you from any data leak or hacking campaign thanks to virtual agents.
Once your breaches have been fixed, an HTTPCS Certification Seal will be displayed on your website. It will show your visitors your optimal level of security. Sure, we don’t give you a real medal, but it’s close enough!
Don’t wait any longer to carry out frequent and automated audits! By becoming a user of the HTTPCS suite, benefit from a daily protection against hackers!
