Beware the coronavirus and hackers!
In these times of coronavirus, hackers use many trick to steal your money.
Yes, you are about to read an umpteenth article about the coronavirus.
And no, this is not another warning about the virus and social distancing.
As you may know, cybersecurity: it’s our job (subtle product placement). And if I’m writing this article today, while many of us are currently into quarantine, it’s because of a disturbing phenomenon striking the world of cybersecurity: cyberattacks relating to the coronavirus.
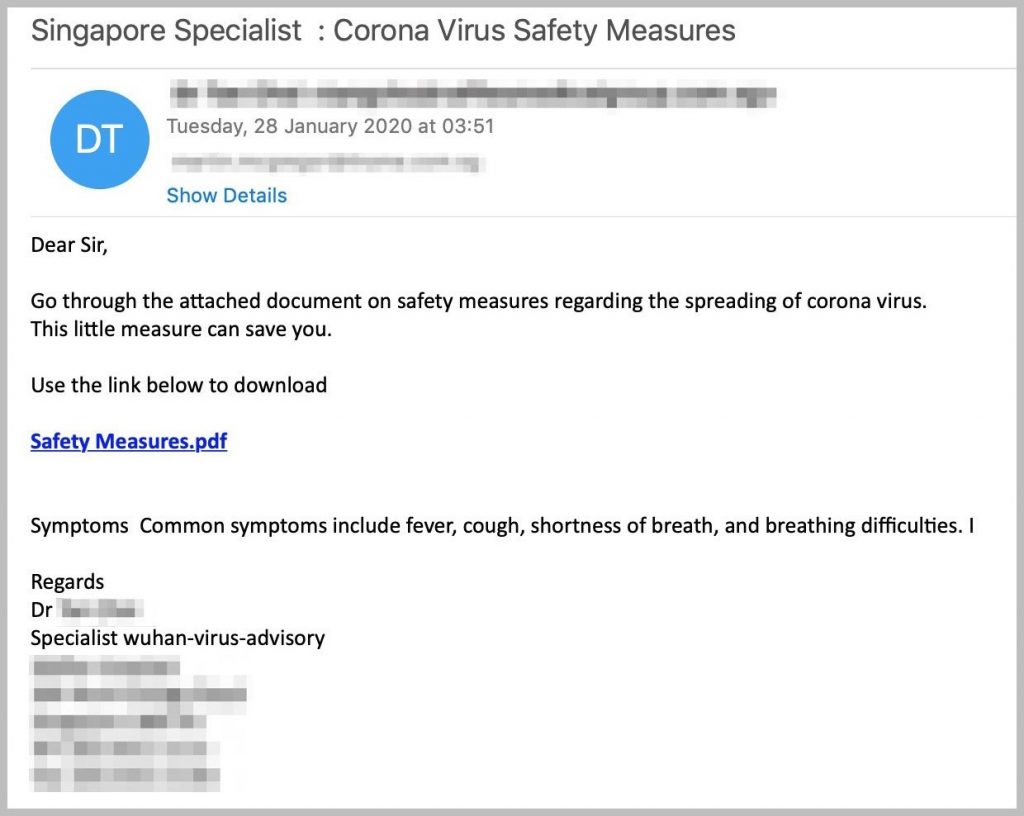
Maybe you didn’t witness this phenomenon yet, but currently, hackers are taking advantage of the coronavirus by carrying out phishing campaigns. Yes, you heard me right, they’d do anything to make some money…
What’s phishing?
Phishing is one of the most popular cyberattacks on the internet. We already talked about it on this blog, but you can still take a look at it if you don’t know anything about this cyberattack technique.

To sum this up in a very simple way, phishing aims to extort personal information, especially your bank details. Hackers are willing to try anything to get your credit card number.
Have you ever received an email from a Nigerian Prince who’s stuck abroad and doesn’t have any money to get back home? Have you ever won a prize you never asked for? Has your carrier ever asked you if you want a refund because of an excess payment? No, this has nothing to do with a good fairy who wants to spread joy. It just means that you’re being targeted by a potential scam.
What are the coronavirus phishing campaigns going around?
With the virus rising and the general feeling of panic, some hackers saw an opportunity to make some money while staying home (as usual for them). Basically, we can’t really hold it against them, they just “seize the day”. Carpe diem, as they say.
Many cyberattack attempts are currently happening. Some of them are intended to get your bank details, while others will try to infect your computer with a virus.
For instance, many Italians received emails that seemed to come from the government to give them safety instructions about their quarantine. Their message contained an attachment that you had to open to get these precious instructions… but it turned out to be a malware called TrickBot. Anyway, you get it: the Italian government did not send this email.
Moreover, other users got tricked by a fake email from WHO, asking citizens to give some money for the coronavirus solidarity fund. Unfortunately, WHO said that these messages were fraudulent, and the organization also took the time to remind people of the good practices in case of phishing.
North Korea also tried to wreak havoc with its Southern neighbor by putting a malware in documents detailing South Korea’s response to the coronavirus. This malware is called BabyShark.
To stop these cyberattacks, some public authorities decided to communicate on that subject in order for you to not take the bait. That’s what the National Cyber Security Centre did in the UK through a press release.
How to recognize a phishing attempt?
Let’s get straight to the point: there is no magic bullet to detect phishing.
The only way to get rid of this threat is to be careful. In order to do this, you must have an eye for detail, because you’ll be able to figure out that it’s a scam thanks to some clues. Here are some tips:
- Check the email address: see if it’s an address with an official domain name.
- Look out for the spelling in the message: fortunately, hackers are generally more good at hacking than spelling. If you receive a message containing spelling mistakes, your “spidey-sense” should be tingling. It’s probably a scam, so check the authenticity of the message.
- Control your over-excitement: if you get a message aiming to sell a cure for coronavirus and starvation around the world, just frown. Put things into perspective, because it’s highly likely that it’s a scam. Same thing goes for any message saying that you won a blue iPhone 5c.
- Don’t disclose your personal data: before giving away your credit card number to anyone, make sure that it’s really necessary. For example, if you get a message from your carrier asking you if you want to get a refund because of an overpayment, it’s probably a phishing message since your carrier is already supposed to have your bank details.

Here’s the watchword: don’t be gullible! If you receive a message about the coronavirus, check its authenticity. Hackers take advantage of the current global crisis through people’s distress. That’s why you have to keep your cool and put those messages into perspective.
What do you have to do if you’re targeted by a phishing campaign?
If you receive a fraudulent message and you don’t know what to do, it’s easy as pie (hello, out of style expression)! Follow this three-step tutorial:
- step 1: read the fraudulent message.
- step 2: delete the said fraudulent message.
- step 3: that’s about it…

In short, if you identified a phishing attempt, that you didn’t give any personal information and that you didn’t open any suspicious attachment, you can relax. Just delete the message and go make fun of the hacker’s level of grammar.
In contrast, if you got tricked, it’s hard as coronavirus (I tried to find the opposite of “easy as pie”, but I couldn’t find it).
Well, if you got tricked by a hacker, it’s okay: this kind of situation happens very frequently. You just need to stay calm and warn the competent authorities. In order to do this, many countries provide a website on which you can lodge a complaint, whether you are an individual or a professional. A trained team will try to find the person behind the scam.
For a business, this kind of situation can have huge consequences over your company. If you suffered a phishing or ransomware attack, the Ziwit experts can save the day. Thanks to the “Incident Response” crisis unit, our cybersecurity experts will tell you what to do and will try to back up your data.
